
In today’s technology-driven world, information/data is one of the most significant assets to every business and industry model. It is an evenly necessary element required to make or break the security mechanism of any organization’s assets, network, or application. From healthcare to the education system, every industry is on the radar of cyber-attacks, and information is the crucial element that cybercriminal goes after.
Open-source intelligence (OSINT) plays a vital role in information collection, which helps everyone, including cybercriminals, security professionals, technical and non-technical individuals, to gather their desirable data and information.
This blog post aims to answer some of the fundamental questions around OSINT that confuse most cybersecurity beginners and non-technical cybersecurity professionals.
OSINT- Open Source Intelligence is another name for collecting information from the internet and other publically available resources. This includes the techniques to classify a large amount of data to determine important or relevant information to achieve a specific purpose. The goal of accumulating information varies from person to organization objectives.
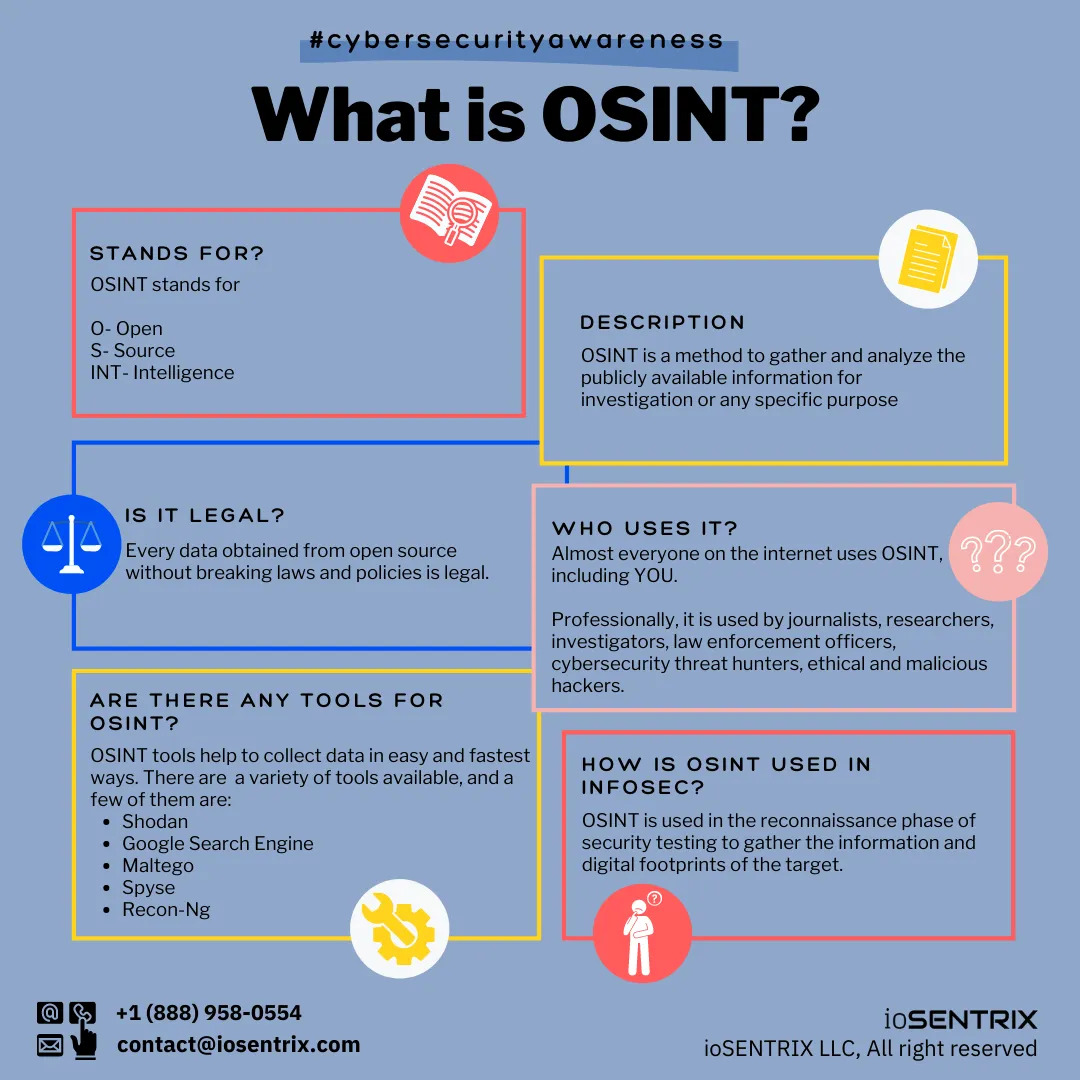
OSINT finds digital footprints that are publicly accessible in any format, including videos, images, conferences, research papers, webinars, etc. It is recognized as a legal activity as long as the person does not break the law, jeopardizes an individual’s privacy, or violates the copyrights.
In cybersecurity, OSINT helps discover compromised and breached credentials, publically available business records, individuals or organization’s personal and background information, documents, image-focused searches, email, and domain information, inter-connected devices or applications information, exploits archives, removed but indexed data, geolocation information, darknet resources, blogs, news, social media content or profiles, etc.
OSINT findings have a broad scope and are not limited to cybersecurity only. Currently, OSINT is being used professionally in every major to minor industries, from healthcare to the education system; everyone relies upon publicly available and usable data.
Other than cybersecurity, it is highly used by journalists, military persons, law enforcement officers, students, researchers, writers, investigators, cybersecurity professionals, and you name it.
Just like everything comes with pros and cons, OSINT can be used in both ways. Notably, in ethical hacking, OSINT helps discover the digital footprints in various cybersecurity assessments such as penetration testing, red teaming, social engineering, threat intelligence, etc.
While utilizing the publicly available information, security professionals and organizations identify sensitive, exposed information that could allow any ill-intentioned hacker to use and launch an attack on the critical assets.

Similarly, in black-hat hacking, malicious attackers use open-source intelligence (OSINT) to retrieve information about their target in order to pick potential vulnerable or beneficial access points that could help them gain data, information or identify a roadmap to develop an attack plan.
For example, Breached credentials play a significant role in tracking organization leaked data and platforms that the companies utilize. It also helps attackers find relevant information to prepare an attack.
In parallel, social networking sites could be a great help for an attacker to identify potential employees of its targeted person or organization. By gathering information of the employees such as email, contact number, designation, etc., he can launch a phishing or smishing attack to trap the individuals with misleading information, forged links, and gain access to the system or steal the credentials.
OSINT has a significant role in identifying internal and external threats and vulnerabilities in any organization’s digital environment and its assets. In information security, for most of the assessment (e.g., penetration testing, red team assessment), information gathering is the first step of security testing. This step is usually termed Reconnaissance in the information and cybersecurity sector.
While doing the reconnaissance, the ethical hacker/security expert collects information about the target such as domain, subdomain, person, organization, and employee’s sensitive identificational information, inter-connected devices, open ports, software, public business records, the website listed directories, and other exposed assets as well as leaked information, e.g., employees’ credentials, business secrets/records, etc. in any previous breaches or available over the dark web to identify the sensitive, exposed data, vulnerable access points, and security gaps to mitigate them.
Open-source intelligence makes it easy to collect all this information in the fastest and easiest way. The same reconnaissance helps make digital footprints against the target; depending upon the approach, it could be active or passive. Many researchers and security professionals usually follow the passive process as it does not let the target know about the activity, nor it alerts the blue team. This is where all security researchers and experts use open-source intelligence (OSINT) in the InfoSec domain.
For instance, In social engineering assessment, security professionals look out for employees’ details such as social media and other application profiles, e.g., Trello, Dropbox, Outlook, etc., to track their activities for phishing, SMShing attacks. In the same manner, exposed and compromised credentials help launch various password attacks, e.g., credential stuffing, brute-force attacks, etc., to have malicious access to systems, applications, servers, etc.
Likewise, in a defensive approach, the threat intelligence team of the organization or individuals can keep track of their data and secrets by utilizing open-source intelligence about whether they have been leaked or exposed. If employees or any other sensitive credentials have been breached or disclosed in any cyber-attack or data leak, they can quickly reset the password and deploy the security controls.
Organizations use the OSINT methodologies to collect all publically accessible information to analyze the data and perform the threat intelligence. Using the right approach to OSINT, if interpreted rightly, the organizations can have the contextual understanding of exposed and usable information that helps analyze the damage and risk of being attacked through the data.
A massive amount of sensitive or publically available data can be accumulated by companies and businesses, which they can sniff out to classify sensitive data and plan the security or data protection model accordingly.
There are numerous OSINT tools, below-mentioned are some of the resources that can be used to collect information:
Google- An essential element of OSINT, if you learn the art of googling, you already completed 85% of OSINT research.
Other than google, one can use
Once the information is gathered, the attack surface can be identified by classifying the data, and the same information can be used to launch potential attacks. There are numerous kinds of cyber-attacks that an attacker can plan and launch depending upon what kind of information he has gathered and his motive.
Following are some of the attacks that can be leveraged in planning some initial and low-high level attacks.
Social Engineering is one type of cyberattack that does not include any high level of technical competencies and relies upon human manipulation techniques. In it, the attacker collects some vendors’ information or employees’ details such as designation, job roles, email addresses, etc. With the help of such information, he’d be able to launch different types of physical or digital social engineering attacks to invade the organization’s remote or on-premises environment.
The most common social engineering techniques involve:
A phishing attack is usually carried out through deceptive emails forged with malicious URLs, attachments, or fake scenarios to manipulate humans in downloading the files, opening links, or giving away sensitive information and credentials . To carry out a phishing campaign, little research on the target is beneficial. Let’s understand it this way.
In phishing emails, the cybercriminals use leaked or breached resources to collect emails, phone numbers, and relevant organization resources to send phishing emails. Phishing emails have hidden malicious software in the form of URLs and attached documents or images. Once the user clicks a link or opens the phishing email file, the malicious software activates itself to steal credentials (user name, password), bypass the security measures, or take the system hostage by utilizing the system owner access.
Many businesses and applications integrate open-source software into their infrastructure. In open-source software, all issues are publicly available, and it is easy to find out loopholes and issues in them. As the source code is available, threat actors can easily exploit or modify it to perform illegal activities by changing code or inserting malware to steal sensitive data or carry supply chain attacks.
Simultaneously, many legitimate extensions and applications scan the website and reveal the platform and technology on which websites or applications are built. This helps the attacker to know about web technology while crafting their attack plans.
Unpatched vulnerabilities impose high risk over the applications, network, and overall IT infrastructure. Every other day vulnerabilities are awarded CVEs, whose exploits and related information are made publically for organizations to understand the severity and patches. With the same information, any malicious hacker can also exploit the bug instead of patching it.
Once the attacker identifies the zero-day vulnerabilities or an unpatched bug present in the system or software, he can then leverage that into exploiting them directly or indirectly. For an instance, suppose an attacker identifies the website CMS version along with some of the CMS 0-days vulnerabilities.
Depending upon the type of flaw, the attacker can access the internal network or steal sensitive data through it.
In this blog, we have discussed a few opportunities for OSINT in identifying and exploiting threats. OSINT is a significant part and also a broad domain in cybersecurity. It wouldn’t be wrong if we say OSINT is a pillar of the cybersecurity industry.
Looking for Part 2 of the blog? Click here
Get in touch with our cybersecurity experts for consultation or discuss the cybersecurity concerns of your business. Meanwhile, wait for our second part of the OSINT blog series to understand OSINT through a practical approach.